Cloud Security
The move to remote work and cloud adoption can result in lack of visibility into cloud security risks, especially as small teams need to support hybrid on-premises and cloud services. Protect your cloud environments, including AWS and Azure with Blumira
Detect & Respond to Cloud Threats
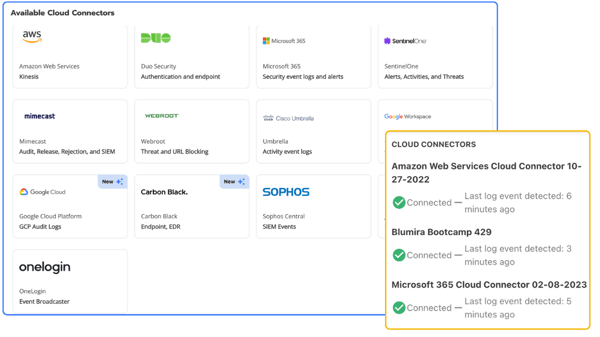
Blumira cloud SIEM can be deployed in minutes with Cloud Connectors, easily integrating with cloud services to detect cloud threats immediately. Respond quickly with Blumira security playbooks that help guide you through remediation.
Quickly detect and respond to cloud security threats with integrations for AWS, Azure and more. Try it out with Blumira Fee SIEM — choose up to 3 cloud integrations, including Microsoft 365, Duo Security, Umbrella, SentinelOne, Webroot and Mimecast.
SIEM For Cloud Security
By centralizing and correlating log data, a SIEM system provides real-time visibility into the security posture of the cloud environment, allowing for prompt incident response and mitigation of security risks.
-
AWS Cloud Monitoring
Cloud Infrastructure Monitoring
Monitor your cloud infrastructure from one centralized dashboard. Detect common security misconfigurations and threats, send prioritized alerts to reduce the noise, and enable your team to take action to remediate.Blumira easily integrates with AWS and Microsoft Azure to detect device malware and enable you to respond to limit its security impact on your environment.
-
Secure Identity & Access
Duo, Okta & Azure AD Security Monitoring
To support a remote workforce, you need secure remote access. Blumira integrates with identity providers to monitor two-factor authentication, endpoint and single sign-on (SSO) and alert you to any potential threats.
Blumira’s cloud-based security leverages threat intelligence and behavioral analytics to detect attacker attempts to log in to your systems, including geo-impossible logins and fraudulent login attempts that could indicate the theft of usernames and passwords.
-
Secure Cloud Collaboration
Google Workspace & Microsoft 365 Security Monitoring
Organizations rely on cloud collaboration tools for employee productivity, working from wherever they are. But without visibility into anomalous access attempts, external document sharing, email forwarding, etc., they can be easy targets for attackers.
Blumira integrates natively with Google Workspace and Microsoft 365 to collect and parse security logs, then monitor and analyze them for potential threats. We alert you to key findings, reduce false positives and provide actionable insights.
-
Endpoint Security Monitoring
Detect & Protecdt Against Malware
Detecting malware, unknown or blacklisted applications and potentially compromised processes running on devices within your network is key to protecting against ransomware infection, data loss or a data breach.
Blumira integrates with endpoint security providers like VMware Carbon Black and CrowdStrike to detect, alert and enable you to quickly respond to the presence of malicious executables and applications in your environment.
-
Tab Item 5
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Sed at volutpat dui.Content For Tab 5
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Etiam ipsum lorem, sodales eget dui eget, iaculis iaculis lectus. Vestibulum tempus, magna et pulvinar feugiat, arcu elit eleifend urna, id porta diam diam eget ligula.
Cloud Infrastructure Monitoring
Blumira easily integrates with AWS and Microsoft Azure to detect device malware and enable you to respond to limit its security impact on your environment.
Duo, Okta & Azure AD Security Monitoring
To support a remote workforce, you need secure remote access. Blumira integrates with identity providers to monitor two-factor authentication, endpoint and single sign-on (SSO) and alert you to any potential threats.
Blumira’s cloud-based security leverages threat intelligence and behavioral analytics to detect attacker attempts to log in to your systems, including geo-impossible logins and fraudulent login attempts that could indicate the theft of usernames and passwords.
Google Workspace & Microsoft 365 Security Monitoring
Organizations rely on cloud collaboration tools for employee productivity, working from wherever they are. But without visibility into anomalous access attempts, external document sharing, email forwarding, etc., they can be easy targets for attackers.
Blumira integrates natively with Google Workspace and Microsoft 365 to collect and parse security logs, then monitor and analyze them for potential threats. We alert you to key findings, reduce false positives and provide actionable insights.
Detect & Protecdt Against Malware
Detecting malware, unknown or blacklisted applications and potentially compromised processes running on devices within your network is key to protecting against ransomware infection, data loss or a data breach.
Blumira integrates with endpoint security providers like VMware Carbon Black and CrowdStrike to detect, alert and enable you to quickly respond to the presence of malicious executables and applications in your environment.
Content For Tab 5
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Etiam ipsum lorem, sodales eget dui eget, iaculis iaculis lectus. Vestibulum tempus, magna et pulvinar feugiat, arcu elit eleifend urna, id porta diam diam eget ligula.
Blumira Users in Their Own Words
Hear what our customers are saying about Blumira.
“We are solving the issue of lacking trained IT security staffing for our business. With Blumira, we get the benefit of having highly trained security experts and their technology constantly evaluating the security posture of our organization as well as responding to detected threats. Their dedication to our security makes it feel like they are a part of our team.”
John P.
IT Manager
“Blumira can be up and running quickly and at a predictable cost that is way below the cost of dedicating staff to using a traditional SIEM tool.”
David H.
Network Admin
“Blumira takes care of almost all of our log parsing, which eases the burden on a small security team. We centralize logs from firewalls, endpoint protection and identity management providers; with Blumira, we are able to filter only prioritized alerts from these critical services to stave off alert fatigue.”
Brian S.
Director of IT, Security & Operations
Additional Cybersecurity Resources
Get more resources
Introducing Blumira Briefings: Your Weekly Security News Download! 🔔
Read More
XSS: What It Means, How It Works, and How to Prevent It
Read More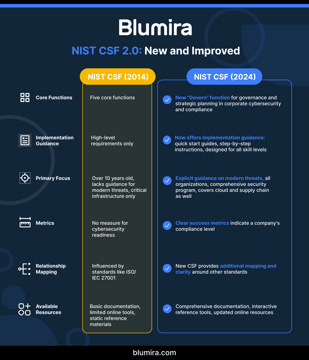
NIST Cybersecurity Framework Implementation for Mid-Market Companies: 2025 Update
Read MoreGet Started for Free
Experience the Blumira Free SIEM, with automated detection and response and compliance reports for 3 cloud connectors, forever.