- Product
Product Overview
Sophisticated security with unmatched simplicityCloud SIEM
Pre-configured detections across your environmentHoneypots
Deception technology to detect lateral movementEndpoint Visibility
Real-time monitoring with added detection & responseSecurity Reports
Data visualizations, compliance reports, and executive summariesAutomated Response
Detect, prioritize, and neutralize threats around the clockIntegrations
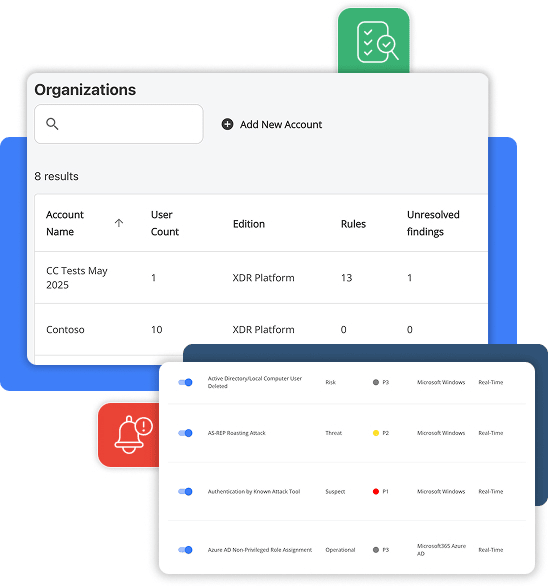
Cloud, on-prem, and open API connectionsXDR Platform
A complete view to identify risk, and things operational
- Pricing
- Why Blumira
Why Blumira
The Security Operations platform IT teams loveWatch A Demo
See Blumira in action and how it builds operational resilienceUse Cases
A unified security solution for every challengePricing
Unlimited data and predictable pricing structureCompany
Our human-centered approach to cybersecurityCompare Blumira
Find out how Blumira stacks up to similar security toolsIntegrations
Cloud, on-prem, and open API connectionsCustomer Stories
Learn how others like you found success with Blumira
- Solutions
- Partners
- Resources
MDR vs. SIEM + XDR
Evaluating security solutions to find the right fit?
Here’s why you may want to choose a SIEM + XDR platform over MDR services.
SIEM + XDR expands visibility beyond just the endpoint while automating the manual, time-consuming, and error-prone work that MDRs must rely on staff to do. SIEM + XDR results in faster, more effective detection and response, while meeting compliance & cyber insurance requirements for data retention.
The Problem With MDRs
MDR (Managed Detection and Response) services offer alert investigation, triaging, threat hunting, and incident remediation. The idea of outsourcing all of your security can be appealing, especially to organizations with limited time or teams. However, MDRs promise a lot with varying degrees of fulfillment.
MDR teams are often overworked and staffed with junior analysts who are spread thin supporting many different clients, which results in poor performance issues and a heavy reliance on human expertise and prioritization across clients. MDR visibility is also often limited to endpoints, which results in missing earlier signals from other data sources that go untracked.
“A lot of MDRs are agent-only, and don’t provide a network component; using only an agent to build context around incidents. Since I can integrate Blumira directly with firewalls, I was alerted to a hacker from Moldova who was conducting password-spraying attacks on a customer’s firewall. I was able to find the IP address and block the attacks completely.”
Aaron Cervasio
Detection Delay
Lack of Control
Lack of Logs & Visibility
The Myth of Fully-Outsourced Security
The Advantages of SIEM + XDR

The Advantages of SIEM + XDR
A SIEM (System Information and Event Management) solution provides a holistic view of your entire environment by collecting and normalizing data from your applications, systems, servers, endpoints, and more to provide continuous security monitoring. A SIEM should retain a complete history of your logs for compliance and cyber insurance.
When paired with XDR (Extended Detection and Response) capabilities, the solution can identify threats, triage events, prioritize findings, and provide both guided and automated response. Automating the manual work of an MDR team results in faster detection and more efficient operations.
Why choose Blumira’s SIEM + XDR platform over MDR services:
-
Fastest Threat Detection

Get notified within a minute of initial detection, with no delay or manual triaging required. Expedite your remediation times and get early breach prevention with auto-deployed detection rules that are updated weekly and focused on signs of attacker behavior that’s correlated across data from many different sources beyond the endpoint.
-
Automation Reduces Work

The average user spends less than 15 minutes a day managing Blumira. Save time spent on manual tasks, and eliminate the need to hire a security team with Blumira’s platform that automates 24/7 monitoring, detection, triaging, notifying, and providing steps for response — as well as automated endpoint isolation to contain threats immediately, no human intervention required.
-
Total Log Visibility & Retention

Gain direct access to your logs with the ability to search, export, and send automated reports, thanks to Blumira’s SIEM which retains a year of complete log history with unlimited data ingestion at a flat fee. Fully intact logs are critical to determine the scope of an incident, helping meet compliance and cyber insurance requirements for data retention.
-
24/7 Security Operations

In addition to an automated platform, you also have access to Blumira’s security team 24/7 to provide guided response, troubleshoot issues, and more when you have a critical issue. With a 99.7% customer satisfaction score and an average 18-minute response time, you can rest easy knowing you’re in good hands.

Get notified within a minute of initial detection, with no delay or manual triaging required. Expedite your remediation times and get early breach prevention with auto-deployed detection rules that are updated weekly and focused on signs of attacker behavior that’s correlated across data from many different sources beyond the endpoint.

The average user spends less than 15 minutes a day managing Blumira. Save time spent on manual tasks, and eliminate the need to hire a security team with Blumira’s platform that automates 24/7 monitoring, detection, triaging, notifying, and providing steps for response — as well as automated endpoint isolation to contain threats immediately, no human intervention required.

Gain direct access to your logs with the ability to search, export, and send automated reports, thanks to Blumira’s SIEM which retains a year of complete log history with unlimited data ingestion at a flat fee. Fully intact logs are critical to determine the scope of an incident, helping meet compliance and cyber insurance requirements for data retention.

In addition to an automated platform, you also have access to Blumira’s security team 24/7 to provide guided response, troubleshoot issues, and more when you have a critical issue. With a 99.7% customer satisfaction score and an average 18-minute response time, you can rest easy knowing you’re in good hands.
Since transitioning to the co-managed model and implementing Blumira, IT Manager Paul Silvestri estimates a 60% reduction in support requests.
Blumira’s Managed Detections and Proactive Outreach
To help our customers identify indicators of compromise early and often, Blumira’s
incident detection team manages the detection rules that power our platform.
Tasks include:
Threat hunting & releasing new detections every week
Prioritizing detections for critical security vulnerabilities & exploits
Ensuring actionable findings are sent within minutes (or less) of initial detection
Proactive outreach to customers about malicious activity seen in their environment
Creating custom detections for customers
Assisting in incident response activities during a customer incident
Tuning detections to reduce false positives & noisy alerts
Frequently Asked Questions
What is the difference between MDR and SIEM?
MDR (Managed Detection and Response) is a fully outsourced security service where a third-party SOC monitors your environment and responds to threats on your behalf. SIEM (Security Information and Event Management) is a platform you operate that collects and correlates log data across your environment, giving your team direct visibility into what's happening. The core tradeoff: MDR removes the operational burden but also removes your visibility. With a SIEM like Blumira, you retain full access to your security data while Blumira's 24/7 SecOps team provides expert backup on critical findings.
How much does MDR cost compared to SIEM?
MDR pricing varies widely by provider, but published data gives some reference points. Arctic Wolf's MDR Basic for 100 users lists at $44,000/year on AWS Marketplace, and their EWS Small for 1,000 employees lists at $20,750/year on Azure Marketplace (per marketplace listings, accessed March 2026). Most MDR providers require a sales conversation for exact quotes, so total costs depend on environment size and service tier. A small automotive company evaluated Arctic Wolf MDR alongside CrowdStrike and Splunk, and chose Blumira at less than half the cost of Arctic Wolf (blumira.com/blog/small-automotive-company). Blumira uses flat-rate pricing per employee with unlimited data ingestion, so costs stay predictable regardless of log volume or endpoint count. Both models include security expertise, but Blumira also gives you the detection platform itself, not just the service layer on top.
When does MDR make more sense than running your own SIEM?
MDR is a reasonable choice when your organization has zero internal security staff, no plans to hire any, and needs coverage immediately. If you genuinely cannot dedicate anyone to security operations, even part-time, a fully outsourced MDR provider like Arctic Wolf or Expel handles everything for you. The tradeoff is that you lose visibility into your own environment and become entirely dependent on the provider's detection logic, escalation decisions, and response timelines. Another option for zero-staff organizations is deploying Blumira through an MSP partner, which gives you SIEM visibility and expert management without the black-box limitations of pure MDR.
What are the downsides of MDR?
You lose direct visibility into your security data, the ability to investigate incidents yourself, and control over detection tuning. MDR operates as a black box: the provider decides what's worth escalating and what gets suppressed. You also lose log retention you can search independently, which matters for compliance audits and forensic investigations. With Blumira's SIEM+XDR approach, you get 1 year of searchable log retention, pre-built detections maintained by Blumira's security operations team, and automated response actions that execute immediately rather than waiting for a human analyst in someone else's SOC.
Can I use MDR and SIEM together?
You can, but it creates overlap and cost duplication. Some organizations run an MDR service alongside a SIEM to get both outsourced response and internal visibility, but you end up paying for the same detection twice and managing two separate alert streams. Blumira addresses this by combining the platform (SIEM+XDR with automated response) and expert support (24/7 SecOps team) in a single product. That team provides guided response playbooks for your staff and handles escalations directly, which covers the same ground MDR does without requiring a separate contract.
Is MDR enough for compliance requirements like HIPAA, PCI, or CMMC?
MDR alone often falls short for compliance because auditors want to see that your organization has access to security logs and can demonstrate your own monitoring capabilities. Many compliance frameworks require log retention (HIPAA requires 6 years of documentation retention for policies and procedures (per 45 CFR 164.530(j)), and most compliance advisors recommend matching that retention for audit logs, PCI DSS requires 1 year (per PCI DSS v4.0, Requirement 10.7)). For DoD contractors, CMMC 2.0 Level 2 requires audit log retention aligned to NIST 800-171 AU controls. With pure MDR, those logs live in the provider's environment, not yours. Blumira provides 1 year of searchable log retention and gives your team direct access to findings and reports, which auditors can verify firsthand.
What happens to my security data if I cancel my MDR provider?
With most MDR providers, your historical security data stays with them. You typically lose access to detection logs, investigation records, and incident history when the contract ends. This creates vendor lock-in, and your incident timeline has a gap that auditors and insurers will notice. With a SIEM like Blumira, the data lives in your environment. Your log history, detection records, and incident documentation remain accessible throughout your retention period regardless of contract status.
When is Blumira NOT the right choice compared to MDR?
Blumira executes automated response actions immediately for known threat patterns, but some incidents still require a human to review the evidence and make the call. If nobody on your team can make that call, a fully managed MDR provider handles everything, including the decisions. For very small organizations with no IT staff at all, working with an MSP who manages Blumira on your behalf is a more practical path than either self-managed SIEM or direct MDR.
<
Discover the Blumira Difference
Dive into how Blumira simplifies cybersecurity for IT teams. From setup to real-world use cases, our demo covers everything you need to start your security transformation. No preparation needed, just curiosity.
Request A Demo
(*) Required Fields