Security How-To
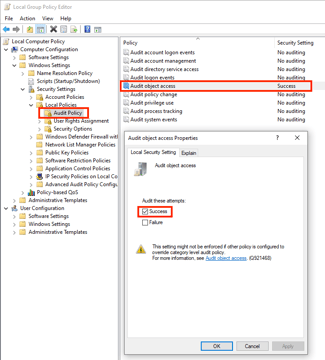
How To Detect File Changes in Windows Server
Read More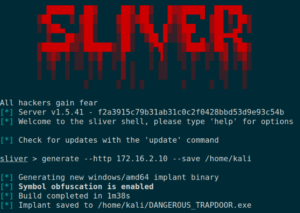
The Hedgehog Defense – Default Apps
Read More
Uncover Threats in Your Windows Environment with Sysmon
Read More
Incident Response for State and Local Governments
Read More
The steps municipalities can take to prepare for rising cyberattacks
Read More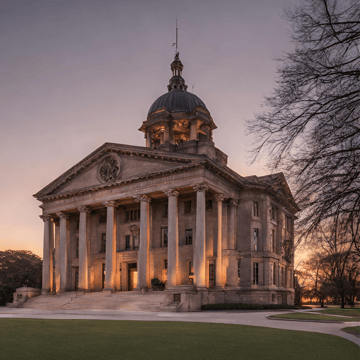
Revolutionizing Government Cybersecurity: Ottawa County’s Journey with Blumira
Read More
4 Unexpected Ways to Strengthen State and Local Government Cybersecurity
Read More
How to Identify and Prevent Phishing in Businesses
Read More
Cybersecurity Detection and Protection—No Matter How You Say it
Read More
How to Get Cybersecurity Buy-in from Executive Leadership
Read More
How Manufacturing Companies Can Prevent Cyber-Attacks
Read More
Blumira’s SMB Cybersecurity Checklist
Read More
ESG: Strategies for Supercharging Security Teams
Read More
Correlating GeoIP Lookups
Read More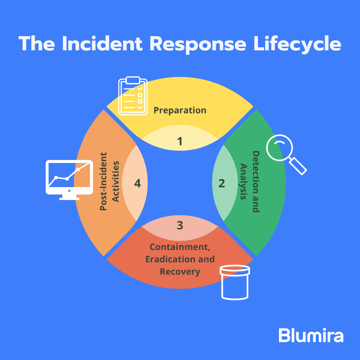
Incident Response Strategies for Ransomware
Read MoreSubscribe to email updates
Stay up-to-date on what's happening at this blog and get additional content about the benefits of subscribing.