Welcome to our weekly security detection and report update. Our Incident Detection Engineering (IDE) Team is constantly hard at work. Creating, testing, and writing detections for you! This week, we've made several important updates to improve your security posture and enhance the functionality of our detections. As you might know, monthly, we also release an overview of the entirety of what was changed in the product. However in these updates we'll focus on the net new content that IDE provides on an ongoing basis, musings from our team, and maybe the occasional horoscope if you're lucky.
Introduction and Overview
Sometimes operational detections can mean just as much as security ones. We do our best to create those to help support your business when we can!
New Detections
This update introduces:
Duo: Bypass Code Created
This could be due to not having their MFA device, losing it, or getting a new one while not having it set up. It also could be a bad actor attempting to bypass MFA requirements or creating an additional authentication option under their control.
- Status: Disabled
- Log type requirement: Duo Admin
Cisco Meraki: System Failover Event
If failovers are happening frequently, it may indicate a persistent issue that needs to be addressed. For more information about Meraki Failover events, see Meraki documentation linked here.
- Status: Disabled
- Log type requirement: Meraki Events
IDE Content
Of course we're going to sneak some of our other content into detection updates!
Cisco ASA and FTD Firewalls Targeted by State-Sponsored Hacking Group “ArcaneDoor”

On April 24th, 2024, Cisco disclosed that a state-sponsored hacking group, dubbed “ArcaneDoor,” has been actively exploiting three zero-day vulnerabilities in Cisco Adaptive Security Appliance (ASA) and Firepower Threat Defense (FTD) firewalls since November 2023. The group has been targeting government networks worldwide, focusing on espionage and gaining in-depth knowledge of the compromised devices. While the attack vector used to provide attackers initial access remains unknown, Cisco has provided details on the specific vulnerabilities used during the hacking group’s campaign.
Amanda Berlin
Amanda Berlin is the Senior Product Manager of Cybersecurity at Blumira, bringing nearly two decades of experience to her position. At Blumira she leads a team of incident detection engineers who are responsible for creating new detections based on threat intelligence and research for the Blumira platform. An...
More from the blog
View All Posts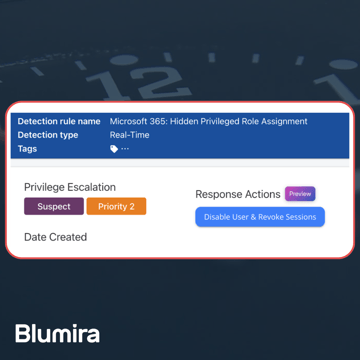
Blumira Launches New Microsoft 365 Threat Response Feature for Faster and More Efficient Security Operations
Read More
Now Available: Microsoft 365 Threat Response From Blumira
Read More
February 2025 Product Releases
Read MoreSubscribe to email updates
Stay up-to-date on what's happening at this blog and get additional content about the benefits of subscribing.