Summary
In August, we released new detection rules for Windows and Entra logs, and we updated the way we allocate Blumira Agents in Managed Service Provider (MSP) accounts with eligible licenses.
Feature and Platform Updates
-
MSP Agent Limits: MSPs with current contracts that do not include any legacy editions (i.e., Cloud or Advanced) now automatically receive two agents per user in the app for sub-accounts on XDR or SIEM+ editions. Sub-accounts on M365 Edition now get 5 agents to experience extended observability and detections for remote endpoints. With our August release, managing limits for Blumira Agent is as easy as updating the user count of the organization from the MSP Portal. We update the maximum agent count automatically, removing the need for partners to manually increase and keep track of the number of agents used by each account. MSP partners can find more details in MSP pricing.
Detection Updates
| Log Type | Detection Details |
|---|---|
|
Windows or Blumira Agent Endpoint |
NEW - Generic Locker PowerShell Module This new P1 Threat detection rule triggers an alert when a Windows device logs activity that matches behavior associated with a script known to be used by threat actors to deploy various ransomware variants. |
|
Windows or Blumira Agent Endpoint |
NEW - File Download from IP URL via Curl.EXE This new P1 Suspect detection rule triggers when a user is seen using a Curl command to download files from an external IP address. Findings include the command used for the download. Curl is a command line tool that is most commonly used to transfer data to and from a server. While it is a useful tool for administrators and developers, it is also used by threat actors to download malicious files and applications from their attack infrastructure. Curl is packaged by default with Windows 10 and higher. |
|
Windows |
NEW - Excessive MSSQL Login Failures This new P2 Suspect detection rule is disabled by default, so it needs to be enabled by an administrator. This rule triggers an alert when a device logs 30 or more failed logins against a MSSQL service on the device within a 1-hour window. This could indicate an attempted brute force attack or a misconfigured service account using incorrect or expired credentials. |
|
Office365 AAD |
Deprecated - Azure: AD Global Admin Role Assignment This legacy detection rule was deprecated and replaced by the two new Entra ID rules described below. |
|
Office365 AAD and Azure Directory Audit |
NEW - Azure: Entra ID Global Admin Role Assignment This new detection rule is a revised version of the deprecated “Azure: AD Global Admin Role Assignment” rule. It is a P1 Suspect rule that is enabled by default when deployed. This rule triggers an alert when a user or group in your Entra ID Directory is assigned a Global Administrator Role. This detection rule excludes assignments done by Privileged Identity Management (PIM) and Granular Delegated Admin Permissions (GDAP). |
|
Office365 AAD and Azure Directory Audit |
NEW - Azure: Entra ID Global Admin Role Assignment by PIM/GDA This new P3 Suspect detection rule is disabled by default, so it needs to be enabled by an administrator. This rule triggers an alert when either Privileged Identity Management or Granular Delegated Admin Permissions (GDAP) assigns a Global Administrator Role to a user or group in your Entra ID Directory. |
| Multi-source |
Reconnaissance via Net Commands Findings for this detection now include the |
July Release Notes
In case you missed the July updates, you can find and review those notes here.
More from the blog
View All Posts
SIEM Starter: A Budget-Friendly SIEM That Meets Compliance & Keeps You Secure
Read More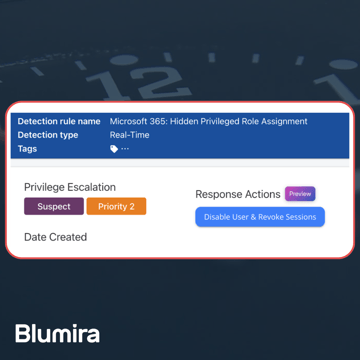
Blumira Launches New Microsoft 365 Threat Response Feature for Faster and More Efficient Security Operations
Read More
Now Available: Microsoft 365 Threat Response From Blumira
Read MoreSubscribe to email updates
Stay up-to-date on what's happening at this blog and get additional content about the benefits of subscribing.